
There Is No New Normal: Cybersecurity’s Two Media Landscapes
Since March, COVID-19 has dominated the media’s attention, highlighting flaws across the medical, political and technological landscapes. With each passing day, references to the “new normal” are thrown around by vendors and reporters alike to, describe the current state of affairs. But cybersecurity communicators, you’ve known for a long time — there is no new normal.
There is nothing normal about pandemics, societal and geopolitical chaos, or election years like we’ve seen in 2020. That said, the sudden, pandemic-driven shift to WFH was a wake-up call to issues and topics that cybersecurity companies have been shouting about for years. Data breaches, insider threats, IoT flaws, phishing scams, cloud misconfigurations … those headaches are NORMAL parts of a security comms pro’s day. The difference is, now more people are talking about these issues. After months of noise (FUD, misinformation and fighting competition for airtime), how do you move forward in an age and industry constantly in disruption?
Earlier this month, the cybersecurity team here at WE Communications had the pleasure of meeting with 20 of the world’s leading cybersecurity comms professionals to discuss media relations trends over the past seven months. We had a lively conversation about the trends bubbling up across 14,000+ articles and 160+ business, tech and security publications. What did we find? 2020 has reshaped cybersecurity’s media landscape, with mainstream business outlets and tech trades covering the industry in new ways.
Business media coverage exploded — but was it relevant?
As expected, there was a massive surge in mass media coverage of cybersecurity, with nearly 6,000 articles during this time. There was a 1,165% increase in WFH and cybersecurity topic coverage. For some, that may give the impression (and perhaps hope) that cybersecurity has finally come into the mainstream consciousness. But, if you dive deeper, business and consumer press coverage was still very superficial. On the other hand, tech trades continued to dig into the specifics of what threats are emerging and the types of technology involved. In mass media outlets, politics and finger-pointing remained the name of the game. Coverage focused primarily on near-term topics, not specific industry threats, and was general in focus.
Nation-state hacking continued to be an issue, and reporters were eager to know where attacks are coming from and on whose orders. The White House doubled down on China as a key player; however, others like Microsoft and those in the intelligence community were concerned about Russia. There was little differentiation on whether the hacks were politically or financially motivated. Other top stories focused on “Zoom bombing,” misinformation, foreign intrusion accusations against Russia and China, the Twitter hack, the Marriott and Uber breaches, and ransomware attacks against health and educational institutions.
Technology trades kept it real
Unsurprisingly, the tech and security media got to the heart of what really mattered this year in cybersecurity. Across 8,000+ articles, these outlets showed more restraint and less political theater, focusing on topics to drive leads and industry conversations.
Although there was a consistent drumbeat of hack and data breach coverage — more than 40 incidents were discussed during this analysis — only a few events, like Twitter, Marriott and EasyJet, saw significant article numbers or multiweek coverage.
One of the biggest surprises, and probably a pain point felt by security companies across the globe, was a drop in reporters picking up data. Vendor reports or surveys were only mentioned in roughly 30% of articles over the past six months. That’s a much lower output than we have seen in previous years, and a shame for the hundreds of hours of manpower that go into compiling these results.
Ransomware was still a major interest among the tech trades (for example, Carnival and Garmin). Other breakthrough topics included NASA and FBI malware warnings, and Google COVID-19 phishing scams. Overall, attacks have become more complex and sophisticated — there is growing interest in ransomware as a service (RaaS), which allows anyone to buy the software needed to launch an attack. Health care, education and manufacturing were of particular interest to these hackers.
Cybersecurity storytelling opportunities in 2021
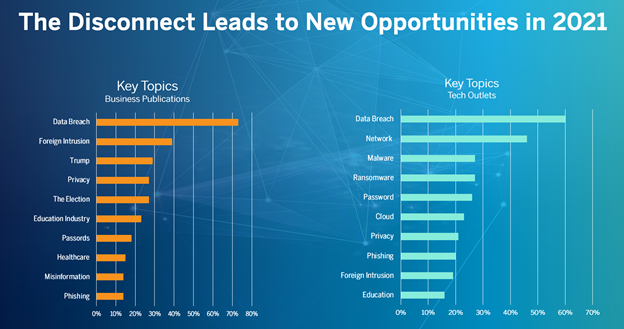
As you digest all of this, you are probably asking yourself an important question, “Now what?” There is a great opportunity to look at these two different media landscapes and see how you can leverage their interests to back into the right story. There is also room to look ahead and plan against the topics, threats and technologies that will be top of mind in the year ahead. Scratch thoughts from our team include:
- Misinformation and disinformation threats won’t disappear on January 20. Although “fake news” may have a specific connotation, the threat of misinformation is real and not slowing down. Cybercriminals and threat actors are already taking advantage of those looking for details on COVID-19 vaccinations. With a playbook created for election mischief, they will continue to exploit an audience struggling with digital media literacy.
- IoT goes from thought leader to market driver. Connected device makers will double down on smart office initiatives to drive employee experience transformation. When connected devices create new opportunities for cybercriminals to find ways into your networks, what does that mean for your business?
- Cloud first matters. Will people finally grasp what cloud is or the shared responsibility it entails? With the rush to move quickly in the digital transformation era, many are leaving behind a crucial understanding of their role in securing cloud data.
- Privacy and location data will fuel the battle of convenience versus protecting personal data. At the end of the day, what is the individual worth? We are more than zeros and ones and should no longer be viewed as only a breach record or statistic.
Let us know if you’d be interested in bringing any of these topics to life; we’d love to speak with you.
The latest blogs from WE
Decoding Gen Alpha: A Primer on the Next Gen of Consumers
Why Gen Alpha Will Fuel Spending This Season
Why Reputation Is a Business Driver in Healthcare

